In 2025, cyber defense without intelligence is blind.
Attackers have become faster, stealthier, and increasingly automated — while defenders rely on real-time threat intelligence (TI) to predict, prevent, and outmaneuver adversaries. This article explores the latest trends, tools, and tradecraft in threat intelligence, helping security leaders make data-driven, proactive decisions.
1. What Threat Intelligence Really Means in 2025
Threat intelligence is not just a feed or a list of IOCs (Indicators of Compromise). It’s the art and science of understanding adversaries — their tools, tactics, motivations, and infrastructure.
In 2025, effective CTI blends:
- Machine learning analytics (for pattern recognition and anomaly detection),
- Human expertise (context, attribution, intent),
- Automated enrichment pipelines (linking open-source, dark-web, and internal telemetry),
- Cross-sector collaboration (ISACs, CERTs, private-public threat sharing).
The global shift toward intelligence-driven security has turned CTI into the brain of modern SOCs.

2. Top Threat Intelligence Trends in 2025
A. AI-Driven Threat Analysis & Adversarial AI
Generative AI now creates polymorphic phishing kits, fake domains, and even code that adapts in real time to bypass detection.
At the same time, defenders deploy AI-enhanced CTI platforms that automatically correlate indicators, predict attack paths, and generate early-warning models.
This arms race between offensive and defensive AI has become one of 2025’s defining cybersecurity battles.
B. Rise of the Dark Web Economy 2.0
The underground is evolving from chaotic forums to professionalized criminal marketplaces.
Ransomware-as-a-Service, deepfake-for-hire, and exploit brokers now use subscription models and customer support — complete with SLA-style guarantees.
Threat intelligence teams increasingly monitor these ecosystems through AI-assisted OSINT, language-adaptive crawlers, and darknet data fusion systems.
C. Nation-State Operations and Hacktivism Resurgence
Geopolitical conflicts continue to blur the line between espionage and activism.
Nation-state actors leverage zero-day stockpiles, wiper malware, and influence campaigns, while hacktivists weaponize social media and data leaks.
CTI analysts must now integrate psychological operations (PSYOPS) monitoring, geo-risk scoring, and deepfake validation pipelines to interpret global events accurately.
D. Intelligence Automation and Maturity Models
According to recent industry surveys, over 70 % of enterprises in 2025 plan to automate at least 60 % of their threat-intelligence workflows — from data ingestion to incident correlation.
Modern CTI platforms integrate directly into SIEM, SOAR, and EDR systems, closing the gap between insight and action.
The key challenge now is quality over quantity: ensuring that intelligence is relevant, verified, and actionable.
E. Cyber Threat Intelligence + Supply-Chain Security
The SolarWinds, MOVEit, and 3CX incidents reshaped how organizations view supply-chain risk.
Threat intelligence now maps trust relationships between vendors, continuously scoring third-party exposures.
Global enterprises deploy threat correlation graphs to trace compromise propagation across dependencies.

3. Building an Intelligence-Driven Defense
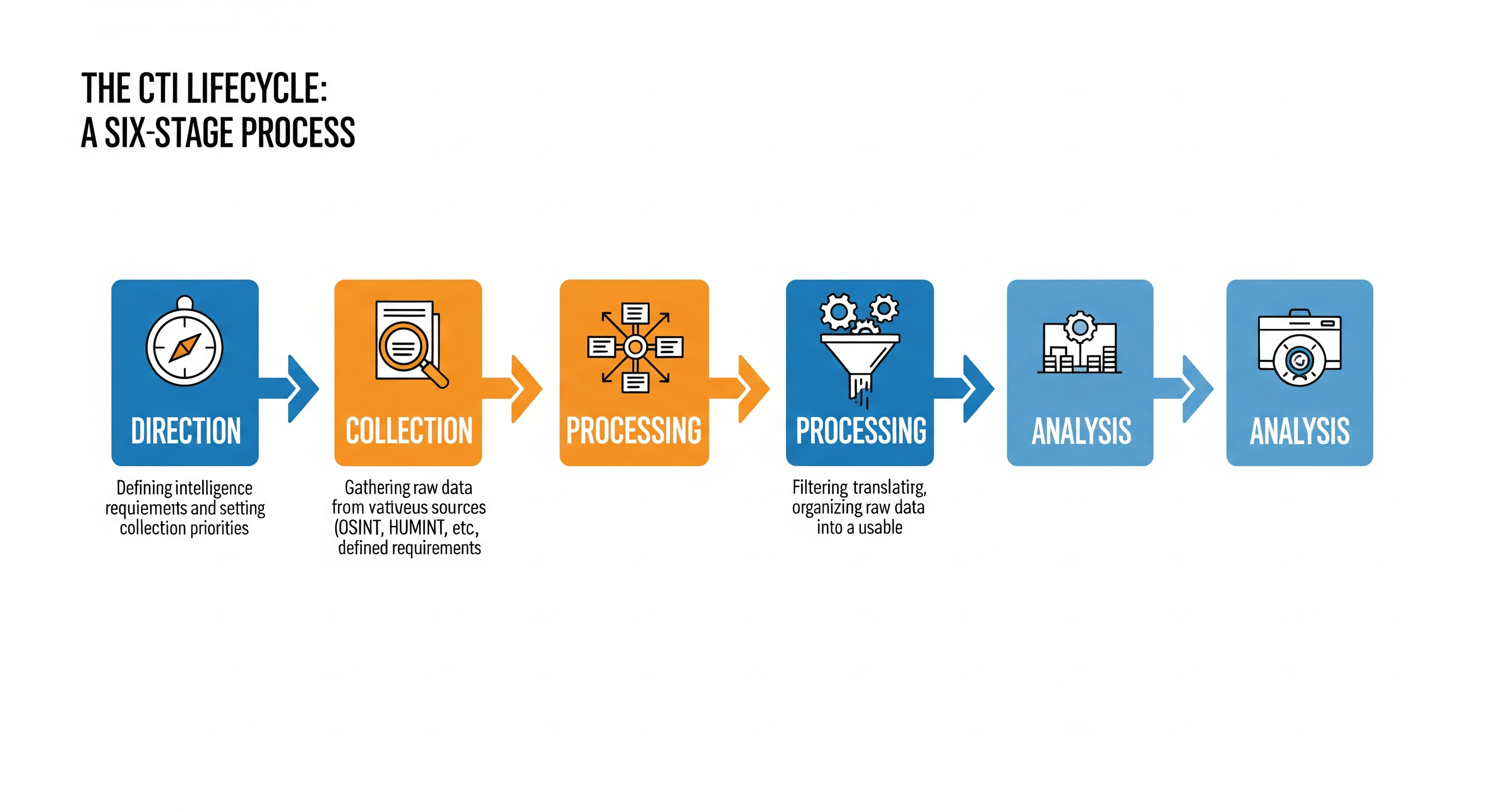
To implement CTI effectively, organizations must follow a structured lifecycle:
- Direction: Define intelligence requirements — who are your most likely adversaries?
- Collection: Gather from diverse sources — OSINT, telemetry, honeypots, dark web, threat feeds, malware sandboxes.
- Processing: Clean, normalize, and deduplicate data.
- Analysis: Use ML and human validation to connect dots and assess intent.
- Dissemination: Deliver intelligence to the right teams at the right time (SOC, IR, management).
- Feedback: Continuously refine requirements based on incident outcomes.
A mature CTI cycle transforms raw data into operational decisions: which alerts to prioritize, which systems to patch first, and which users to train urgently.

4. Practical Use Cases for 2025
| Use Case | Example |
|---|---|
| Predictive Defense | AI models anticipate phishing domains before registration using DNS pattern analysis. |
| Automated IOC Enrichment | Indicators cross-checked with 20+ data sources in seconds. |
| Dark-Web Monitoring | Continuous scanning for leaked credentials or brand mentions. |
| Threat Actor Profiling | Graph databases map TTPs (MITRE ATT&CK) to actor clusters. |
| Executive Threat Briefings | Automated intelligence digests for C-level decision-making. |
5. Tools & Technologies Dominating CTI in 2025
- MISP 3.x / OpenCTI - open-source intelligence management hubs.
- Elastic Security / Splunk SOAR integrations for automated enrichment.
- Maltego + Yeti + IntelMQ - graph-driven link analysis.
- Dark web AI crawlers (synthetic language decoys to infiltrate closed forums).
- Large Language Models (LLMs) fine-tuned on threat-intel corpora for contextual tagging and correlation.
These tools exemplify the convergence of data science and intelligence analysis - enabling defenders to outpace human-scale adversaries.

6. Challenges: The Human Factor Remains the Weak Link
Despite AI and automation, human interpretation remains critical.
Poorly contextualized intelligence leads to false confidence.
CTI teams must cultivate linguistic, geopolitical, and cultural awareness - because motives drive attacks as much as malware does.
Analysts who understand why adversaries act will always outperform those who only see how they act.
7. The Future of Threat Intelligence: Prediction and Collaboration
By 2030, threat intelligence will evolve into Predictive Cyber Defense — where machine learning models forecast adversary campaigns days before they occur.
Shared intelligence hubs (secured via federated learning) will allow organizations to collaborate without exposing raw data.
This collective, privacy-preserving intelligence fabric may become the single most powerful weapon defenders have.
As one analyst from ENISA put it recently:
“The future of cyber defense will depend not on who knows more, but on who shares faster.”
Conclusion — Intelligence as the New Firewall
Threat intelligence has evolved from a luxury to a strategic necessity.
In a world of real-time attacks, speed, context, and collaboration define survival.
Organizations that embed intelligence into every layer of their operations - from network defense to executive decision-making - will not just survive cyberwarfare; they’ll shape its outcome.
The future belongs to those who see threats before they strike - and act decisively.


