The network perimeter is dead - long live the network fabric. In 2025, network security has shifted from castle-and-moat thinking to continuous verification, AI-aware defenses, and risk-aware, identity-first architectures. This article unpacks the biggest trends reshaping network security, explains practical controls, and points security leaders to high-impact actions they can implement today.
Table of contents:
- Executive summary
- Top trends shaping network security in 2025
- Concrete control map: what to implement now
- Practical case studies & playbook items
- Designing for the future: AI, quantum readiness & supply-chain resilience
1. Executive summary
Network security in 2025 is defined by four converging forces: pervasive cloud and hybrid work, generative-AI-driven threats, Zero Trust / SASE adoption, and a widening attack surface from IoT and supply-chain dependencies. Organizations that pair automated, telemetry-driven detection with rigorous identity-centric access controls and supply-chain hygiene will gain a durable advantage. Key statistics and industry observations are cited below.

2. Top trends shaping network security in 2025
A. Generative AI as both weapon and shield
Generative AI has become a dual-use technology: attackers use it to craft highly convincing phishing, generate polymorphic malware, and simulate human voices for BEC/deepfake scams; defenders use it for anomaly detection, automated threat hunting, and response orchestration. Because adversaries now leverage ML to scale social-engineering and code-generation, security teams must validate AI-produced indicators and assume rapid adversary iteration. Recent global cybersecurity outlooks explicitly list GenAI as a top concern for organizations in 2025.
B. Zero Trust & SASE move from pilot to mainstream
Zero Trust Network Access (ZTNA) and Secure Access Service Edge (SASE) architectures continue to replace legacy VPNs and perimeter appliances. The trend is driven by remote work, SaaS proliferation, and the need for fine-grained access decisions based on identity, device posture, and risk signals. Vendors and MSSPs are packaging SASE + XDR offerings to simplify adoption for mid-sized and large enterprises.
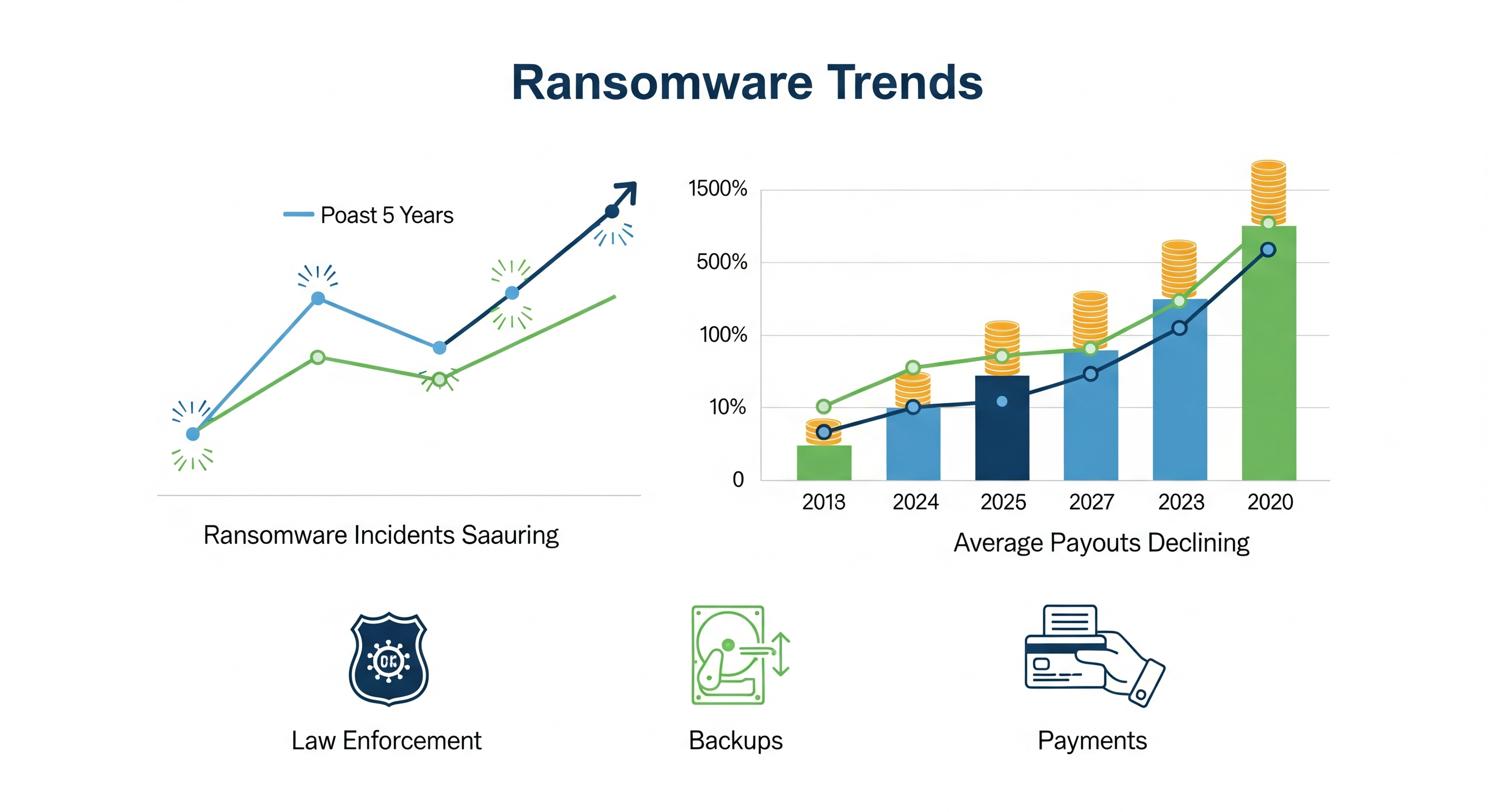
C. Ransomware evolved: more incidents, fewer big payouts (but big risks remain)
While the number of ransomware incidents kept rising, global ransomware payments fell significantly in recent reporting as law-enforcement actions and better defensive readiness reduced payouts. Attackers shifted to extortion, double-extortion and targeted high-value supply-chain victims. This dynamic makes resilience (backups, immutable storage, tested playbooks) as important as prevention.
D. Supply-chain & software-update risks remain critical
Supply-chain compromises (third-party SDKs, CI/CD pipelines, managed services) continue to cause cascading outages and data breaches. Organizations must implement SBOMs, strict dependency controls, and runtime integrity checks to reduce blast radius from downstream compromises. National CERTs and NCSC guidance stress preparedness for these attack vectors. ncsc.gov.uk +1
E. IoT / OT attack surface grows — segmentation matters
The proliferation of IoT and industrial OT devices expands the network attack surface and attracts botnets and ransomware targeting operational systems. Monitoring, microsegmentation, and dedicated OT/IoT network telemetry are now operational imperatives for industries that rely on physical assets.

3. Concrete control map — what to implement now (practical, prioritized)
Priority 1 — Identity & access controls
- Deploy ZTNA for high-value apps; retire legacy VPNs where possible.
- Enforce MFA, short-lived credentials, conditional access (device posture + geolocation).
- Continuous session evaluation (re-check identity + device posture during sessions).
Priority 2 — Telemetry & detection
- Centralize network telemetry into a scalable analytics pipeline (flow logs, proxy logs, DNS, endpoint telemetry).
- Apply ML/behavioral baselining to spot account compromises and lateral movement.
- Use continuous validation / purple-team exercises to test detection fidelity.
Priority 3 — Resilience & recovery
- Immutable backups, air-gapped copies, and rehearsed recovery runbooks.
- Data classification and prioritized recovery tiers to shorten RTOs/RPOs.
Priority 4 — Supply-chain & software hygiene
- Enforce SBOMs and supply-chain risk scores for third-party components.
- Harden CI/CD pipelines (signing, artifact allowlists, ephemeral build agents).
Priority 5 — IoT/OT protections
- Microsegment IoT from enterprise networks; use dedicated visibility tools.
- Implement anomaly detection for device behavior and restrict remote management channels.

4. Practical playbook snippets (short recipes)
Rapid compromise triage (first 60 minutes):
- Isolate the affected segment (network quarantine + revoke sessions).
- Snapshot forensic evidence (flow logs, endpoints).
- Identify initial access vector (phish, vulnerable service, supply chain).
- Notify legal & execs; engage IR partner if needed.
- Begin recovery plan in parallel with containment.
Phishing/AI-driven social engineering mitigation:
- Add multi-channel verification for wire transfers (out-of-band calls).
- Train teams on new AI-generated voice/text signals (supply examples).
- Deploy secure browsing/containerized sessions for high-risk workflows.
5. Designing for the future: AI, quantum readiness & strategic investments
AI security ops (AIOps for SOC):
- Invest in tooling that augments analysts: prioritization, triage automation, auto-containment playbooks. Validate models regularly to avoid adversarial blind spots.
Quantum and crypto agility:
- Begin asset inventories for systems relying on public-key cryptography; plan crypto-agility for certificates and long-lived data that must remain confidential post-quantum.
Vendor consolidation vs. diversity:
- Evaluate risk trade-offs: single vendor SASE stacks simplify telemetry correlation; diverse stacks reduce single-supplier risk. Adopt a hybrid approach aligned with risk tolerance.

Conclusion - Building a Network Security Culture That Lasts
In 2025 and beyond, network security is not just an engineering discipline - it’s a culture of verification, resilience, and adaptability.
Firewalls, proxies, and intrusion prevention systems are no longer enough when the very definition of the “network” stretches across clouds, devices, and APIs. The new perimeter is identity, data, and trust.
Security leaders must align technology with human awareness and business outcomes. The most successful organizations will:
- Integrate security by design into every network decision.
- Automate everything repetitive - detection, patching, validation - freeing experts to focus on strategic risks.
- Invest in cyber-resilience: backups, redundancy, tabletop exercises, and adaptive risk modeling.
- Foster collaboration between blue and red teams - continuous learning closes the loop faster than any vendor patch.
- Educate every employee to recognize that security is everyone’s responsibility.
The shift toward Zero Trust, SASE, and AI-powered analytics is only the beginning. Over the next decade, quantum-resistant cryptography, autonomous SOCs, and policy-as-code infrastructures will redefine what “secure networking” truly means.
At its heart, network security remains a human challenge — one that demands creativity, vigilance, and a mindset of continuous verification rather than blind trust. Those who master this balance will not just defend their networks - they’ll empower their organizations to innovate safely in a hyper-connected world.


